Research topics at CRoCS
How to get involved
- Find project you like,
- Contact people involved,
- Have fun while saving the world (of research and open-source)!
Join us! We are always looking for enthusiastic people with passion for problem solving willing to work hard yet having good fun. Don't be afraid if you don't have previous experience in the project area you like. We are here to help you and we all learn something in the process.
Read the research domains to get a wider picture. Check currently open topics in IS, but do not hesitate do discuss different ones with contact person listed below.
Security of cryptographic implementations
We systematically analyze the security of cryptographic implementations, including the blackbox ones with no access to a source code (e.g., cryptographic smartcards). Typically, a large number of cryptographic operations is executed with observed data and various side-channel information recorded and statistically analyzed. The approach leads to several high-profile discoveries, including the practical factorization of RSA keys from Infineon chips (ROCA attack CVE-2017-15361) or EC private key extraction from timing of ECDSA signatures (Minerva attack CVE-2019-15809). The goal is not only to find an attack but also to provide open-source verification tools.
Contact: Jan Jančár j08ny@mail.muni.cz
More information, projects and resources:
- ROCA online Tester: A tool for testing RSA keys for the ROCA vulnerability.
- ROCA repository: A code repository with the testing tool for the ROCA vulnerability.
- Minerva repository: An artifact repository for the Minerva vulnerability.
- ECTester: A tool for testing blackbox elliptic curve cryptography implementations on smartcards and in software libraries.
- pyecsca: Python Elliptic Curve Cryptography Side-Channel Analysis toolkit.
- Fooling primality tests repository: An artifact repository for the “Fooling primality tests on smartcards” paper.
- 4p-1 repository: An artifact repository for the “I Want to Break Square-free: The 4p−1 Factorization Method and Its RSA Backdoor Viability” paper.
Involved people:
- Łukasz Chmielewski 2022-now (side-channel and fault injection security of crypto implementations)
- Jan Jančár 2017-now (security of ECC implementations)
- Vladimír Sedláček 2017-now (theory)
- Marek Sýs 2013-now (project concept, results interpretation)
- Petr Švenda 2008-now (project lead, initial implementation)
Former participants: Dušan Klinec 2015-2021 (RSA certificates, cryptocurrency security), Matúš Nemec 2016-2021 (bias in RSA key generation),
Selected publications:
- [2025] Suchánek, V.; Kvapil, J.; Jančár, J.; Švenda P.; Chmielewski, L.: ECTester: Reverse-engineering side-channel countermeasures of ECC implementations, In IACR Transactions on Cryptographic Hardware and Embedded Systems, Ruhr-University of Bochum, 2025.
- [2024] Jančár, J.; Suchánek, V.; Švenda P.; Sedláček, V.; Chmielewski, L.: pyecsca: Reverse engineering black-box elliptic curve cryptography via side-channel analysis, In IACR Transactions on Cryptographic Hardware and Embedded Systems, Ruhr-University of Bochum, 2024, 355–381. Received Honorable mention and Best Artifact Award
- [2020] Jančár, J.; Sedláček, V.; Sýs, M.; Švenda, P.: Minerva: The curse of ECDSA nonces; Systematic analysis of lattice attacks on noisy leakage of bit-length of ECDSA nonces, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2020. Received Best Paper Award
- [2020] Klinec D.; Matyas V.: Privacy-Friendly Monero Transaction Signing on a Hardware Wallet, In IFIP TC 11 International Conference (SEC) 2020.
- [2020] Sedláček, V.; Jančár, J.; Švenda, P.: Fooling primality tests on smartcards, In 25th European Symposium on Research in Computer Security (ESORICS) 2020.
- [2020] Janovský, A.; Nemec, M.; Švenda, P.; Sekan, P.; Matyas, V.: Biased RSA private keys: Origin attribution of GCD-factorable keys, In 25th European Symposium on Research in Computer Security (ESORICS) 2020.
- [2019] Sedláček, V.; Klinec, D.; Sýs, M.; Švenda, P.; Matyáš, V.: I Want to Break Square-free: The 4p−1 Factorization Method and Its RSA Backdoor Viability, In Proceedings of the 16th International Joint Conference on e-Business and Telecommunications (ICETE 2019) - Volume 2: SECRYPT
- [2017] Nemec, M.; Sýs, M.; Švenda, P.; Klinec, D.; Matyas, V.: The Return of Coppersmith's Attack: Practical Factorization of Widely Used RSA Moduli, In Proceedings of ACM CCS 2017, 2017. Received Real-world Impact Award
- [2016] Švenda, P.; Nemec M.; Sekan P.; Kvasnovsky R.; Formanek D.; Komarek D.; Matyas V.: The Million-Key Question – Investigating the Origins of RSA Public Keys, In Proceedings of USENIX Security Symposium 2016, Usenix, 2016. Received Best Paper Award
Usability of cryptographic APIs and tools
This project focuses on the cryptographic APIs and tools with respect to their developer usability. Such APIs are notoriously complex and prone to usage errors – our goal is to analyze their (in)correct usage and propose precautions and guidelines to achieve better usability and security.
In the past the research focus was on usable interfaces of cryptographic libraries from the point of developers and administrators lacking detailed security education. We are interested in both programmable and command-line interfaces, with the emphasis placed on X.509-capable libraries, such as OpenSSL, GnuTLS and NSS, paying special attention to the process of certificate creation and validation. The goal is to enable the developers to use security APIs errorlessly and API designers create better interfaces less prone to misuse. We emphasize the necessity of a usable design even for tools targeted at experienced users.
Recently, we also focused on tools for cryptographic developers, such as tools for verification of constant-timeness.
Contact: Vašek Matyáš matyas@fi.muni.cz
- Research project internal wiki pages
Involved people:
- Martin Ukrop 2016-2022
- Jan Jancar 2022-now
- Vašek Matyáš 2016-now
- Lydia Kraus 2018-now
Former participants: Agáta Kružíková 2019-2024.
Selected publications:
- [2024] Fourné M., De Almeida Braga D., Jancar J., Sabt M., Schwabe P., Barthe G., Fouque P., Acar Y.: “These results must be false”: A usability evaluation of constant-time analysis tools, USENIX Security 2024.
- [2022] Jancar J., Fourné M., De Almeida Braga D., Sabt M., Schwabe P., Barthe G., Fouque P., Acar Y.: “They’re not that hard to mitigate”: What Cryptographic Library Developers Think About Timing Attacks, IEEE S&P 2022.
- [2022] Ukrop M., Balážová M., Žáčik P., Valčík E., Matyas V.: Assessing Real-World Applicability of Redesigned Developer Documentation for Certificate Validation Errors, EuroUSEC 2022.
- [2019] Ukrop M., Kraus L., Matyas V. and Wahshehand H.: Will You Trust This TLS Certificate? Perceptions of People Working in IT, ACSAC 2019.
- [2018] Ukrop M. and Matyas V.: Why Johnny the Developer Can't Work with Public Key Certificates, RSA Conference Crytographers' Track 2018.
Security of cryptographic hardware (smartcards, TPMs...)
For more than two decades, we analyze the security of cryptographic hardware and interesting uses in security systems as a trusted element. We work mainly with JavaCard based cryptographic smart cards and Trusted Platform Modules (TPMs). We maintain a large collection of JavaCards and use them to assess their performance, quality of truly random number generators, key generation algorithms as well as security improvements over time. While the internal implementation of cryptographic operations is typically proprietary, we had to develop a suite of techniques for black-box analysis of the implementation correctness - with the advantage of assessment also by other users without the need for proprietary knowledge.
We also develop tools and libraries helping open-source developers to create open, faster, and more secure JavaCard applets.
Contact: Petr Švenda svenda@fi.muni.cz
More information, projects and resources:
- Analysis of cryptographic implementations
- SCRUTINY: tools aggregator GitHib repo
- Classification of RSA key origin based on public key only, accurate popularity of libraries for TLS keys, online checker, classifier of private keys
- ECTester - ECC implementation tester: GitHub repo
- javus - systematic JavaCard VM vulnerabilities testing: Github repository
- Secure hardware performance and capabilities testing
- JCAlgTest GitHub repository - tools for thorough testing of smart card capabilities
- Supported JavaCard algorithms for more then 100 smartcards
- TPMAlgTester project- tools for detailed testing of Trusted Platform Modules
- Smartcard development resources
- Low-level ECPoint and BigInteger library: JCMathLib
- On-card applet performance profiler: JCProfilerNext
- Efficient re-implementations of AES & SHA2 & OAEP for JavaCard, GitHub repo
- APDUPlay project - PC/SC APDU inspection and manipulation tool
- Code Enhancing Security Transformation and Analysis (CesTa) project Github repository - source code hardening via security transformations
Involved people:
- Antonín Dufka 2019-now (MPC on javacards, ECC leakage)
- Veronika Hanulíková 2023-now (ECC leakage)
- Ján Jančár 2017-now (testing of ECC implementations)
- Petr Švenda 2003-now (project lead, initial implementations)
- Łukasz Chmielewski 2022-now (side-channel and fault injection security)
Former participants: Matúš Němec (2015-2020) (analysis of software generated RSA keys); Peter Sekan (2015-2019) (analysis of RSA keys, large datasets); Rajesh Kumar Pal (2016-2017) (JavaCard implementation of CAESAR candidates); Rudolf Kvašňovský 2014-2017 (alignment of DPA traces, YAFU); David Komárek 2015-2016 (power analysis of RSA operation); Lukáš Šrom 2014-2015 (support tests); Lenka Kuníková 2013-2014 (performance evaluation of JavaCards) and quite a lot of other people helping us since 2002
Selected publications:
- [2025] Milan Šorf, Petr Švenda, Łukasz Chmielewski Large-Scale Security Analysis of Hardware Wallets, In International Conference on Availability, Reliability and Security (ARES/TRUSTBUS), 2025.
- [2024] Svenda, P.; Dufka, A.; Broz, M.; Lacko, R.; Jaros, T.; Zatovic, D.; Pospisil, J.: TPMScan: A wide-scale study of security-relevant properties of TPM 2.0 chips, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2024. Received Honorable Mention
- [2024] Jancar, J.; Suchanek, V.; Svenda, P.; Chmielwski, L.: pyecsca: Reverse engineering black-box elliptic curve cryptography via side-channel analysis, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2024.
- [2020] Jančár, J.; Sedláček, V.; Sýs, M.; Švenda, P.: Minerva: The curse of ECDSA nonces; Systematic analysis of lattice attacks on noisy leakage of bit-length of ECDSA nonces, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2020. Received Best Paper Award
- [2017] Nemec, M.; Sýs, M.; Švenda, P.; Klinec, D.; Matyas, V.: The Return of Coppersmith's Attack: Practical Factorization of Widely Used RSA Moduli, In Proceedings of ACM CCS 2017, 2017. Received Real-world Impact Award
- [2017] Mavroudis, V.; Cerulli, A.; Švenda, P.; Cvrcek, D.; Klinec, D.; Danezis, G.: A Touch of Evil: High-Assurance Cryptographic Hardware from Untrusted Components, In Proceedings of ACM CCS 2017, 2017.
- [2016] Švenda, P.; Nemec M.; Sekan P.; Kvasnovsky R.; Formanek D.; Komarek D.; Matyas V.: The Million-Key Question – Investigating the Origins of RSA Public Keys, In Proceedings of USENIX Security Symposium 2016, Usenix, 2016. Best paper award
- [2015] Cvrček, D.; Švenda, P.: Architecture Considerations for Massively Parallel Hardware Security Platform, In Proceedings of Space 2015, Fifth International Conference on Security, Privacy, and Applied Cryptography Engineering, LNCS 9354, pp 269-288, Springer, 2015.
- [2014] Švenda, P.: Nuances of the JavaCard API on the cryptographic smart cards - JCAlgTest project, In Proceedings of ASA 2014, 7th International Workshop on Analysis of Security APIs, 2014.
Cryptanalysis of elliptic curves and other algebraic methods
Likely the most theoretical and math-heavy research we do, though still with real-world consequences in mind. We approach elliptic curves from many different directions: we study ECC implementations, problems with ECC formulas, ECC key datasets, and, in general, diverse mathematical ideas involving elliptic curves. Sometimes, this requires us to dive into lattice methods as well.
Currently, we are mainly focusing on ECC with respect to side-channel attacks, black-box ECC implementations, and the involvement of elliptic curves in the Bitcoin protocol.
Contact: Vojtěch Suchánek vojtechsu@mail.muni.cz
More information, projects and resources:
Involved people:
- Jan Jančár 2019-now
- Vojtěch Suchánek 2020-now
- Marek Sýs 2018-now
- Łukasz Chmielewski 2024-now
- Jan Kvapil 2024-now
Selected publications:
- [2024] Suchánek, V.; Sedláček, V.; Sýs, M.: Decompose and conquer: ZVP attacks on GLV curves, In ACNS - Applied Cryptography and Network Security
- [2024] Jančár, J.; Suchánek, V.; Švenda P.; Sedláček, V.; Chmielewski, L.: pyecsca: Reverse engineering black-box elliptic curve cryptography via side-channel analysis, In IACR Transactions on Cryptographic Hardware and Embedded Systems, Ruhr-University of Bochum, 2024, 355–381. Received Honorable mention and Best Artifact Award
- [2022] Sedláček, V.; Suchánek, V.; Dufka A.; Sýs, M.; Matyáš, V.: DiSSECT: Distinguisher of Standard and Simulated Elliptic Curves via Traits, In Progress in Cryptology - AFRICACRYPT 2022.
- [2021] Sedláček, V.; Chi-Domínguez, J.J.; Jančár, J.; Brumley, B.B.: A formula for disaster: a unified approach to elliptic curve special-point-based attacks, In Advances in Cryptology – ASIACRYPT 2021.
- [2020] Jančár, J.; Sedláček, V.; Sýs, M.; Švenda, P.: Minerva: The curse of ECDSA nonces; Systematic analysis of lattice attacks on noisy leakage of bit-length of ECDSA nonces, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2020. Received Best Paper Award
- [2020] Sedláček, V.; Jančár, J.; Švenda, P.: Fooling primality tests on smartcards, In 25th European Symposium on Research in Computer Security (ESORICS) 2020
- [2019] Sedláček, V.; Klinec, D.; Sýs, M.; Švenda, P.; Matyáš, V.: I Want to Break Square-free: The 4p−1 Factorization Method and Its RSA Backdoor Viability, In Proceedings of the 16th International Joint Conference on e-Business and Telecommunications (ICETE 2019) - Volume 2: SECRYPT
Randomness statistical testing of TRNG and PRNG
The robust generation of truly random data or pseudo-random data indistinguishable from the truly random ones is a crucial component for many cryptographic systems. We focus on finding defects in a supposedly random data with the help of automated testing methods included in so-called randomness statistical testing batteries.
While most existing batteries focus on the predefined fixed tests, we automatically generate tests which adapt to the analyzed data - resulting in a stronger bias detection with a less amount of data required and with direct interpretability of the bias found. We also design and develop means for speedup of existing statistical batteries - both with help of more efficient implementations as well as distributed high-speed execution.
We build and continuously extend a large database of real-world cryptographic functions (CryptoStreams project containing block and stream ciphers, hash functions, PRNGs) parametrized by the number of used internal rounds and systematic patterns in their inputs. The resulting output data are then analyzed for the presence of unwanted defects.
Contact: Marek Sýs syso@mail.muni.cz
Current projects:
- CoolTest/BoolTest - efficient and interpretable statistical testing battery: BoolTest Github repository, CoolTest Github repository
- Randomness Testing Tool (RTT, STS NIST, Dieharder, TestU01) - unified interface for different statistical batteries Github repository
Involved people:
- Marek Sýs 2013-now (CoolTest/BoolTest - concept and improvements, NIST STS speed up, EACirc - concept, results interpretation)
- Jiří Gavenda 2024-now (CoolTest - concept and implementations)
Previous projects and resources:
- Cryptostreams - generator of output data streams from weakened cryptographic functions: Github repository
- Faster implementation of STS NIST testing battery: Online testing service, Github repository
- EACirc - statistical battery based on evolutionary algorithms Github repository, Research project internal wiki pages EACirc wiki pages
Former participants: Milan Brož 2019-2025 (Randomness Testing Tool), Petr Švenda 2008-2017 (EACirc project lead, initial implementation, Cryptostream), Dušan Klinec 2015-2022(BoolTest - polynomial representation, Cryptostream - large number of cryptoprimitives); Karel Kubíček 2014-2017 (Cryptostream - former main developer, block ciphers, TEA, metaheuristics, generator); Tamas Rozsa 2016-2020 (cryptostreams functions); Radka Cieslarová 2015-2019 (heatmap analysis of function); Michal Hajas 2015- 2019 (bytecode emulator, margins); Martin Ukrop 2012-2017 (framework model, refactoring, SHA-3 candidates testing, supporting tools); Ľubomír Obrátil 2014-2017 (BOINC&EACirc tasks automization); Jiří Novotný 2014-2016 (CUDA programming, EACirc core); Jan Švarc 2014-2015 (CUDA programming); Zdenek Říha 2013-2016 (bytecode emulator); Milan Čermák 2012-2013 (CUDA support); Ondrej Dubovec 2011-2012 (SHA-3 candidates testing); Matěj Prišťák 2011-2012 (object model and refactoring, XML support, eStream candidates testing); Tobiáš Smolka 2011-2012 (BOINC related support);
Selected publications:
- [2025] Jiri Gavenda, Marek Sys: CoolTest: Improved Randomness Testing Using Boolean Functions., IFIP SEC, Springer, 2025, vol 746.
- [2022] Marek Sys, Lubomir Obratil, Vashek Matyas and Dusan Klinec: A Bad Day to Die Hard: Correcting the Dieharder Battery, Journal of Cryptology, Springer, 2022, 1–20.
- [2019] Sýs M., Klinec D., Švenda P., Kubíček K.: BoolTest: The Fast Randomness Testing Strategy Based on Boolean Functions with Application to DES, 3-DES, MD5, MD6 and SHA-256, Selected papers of ICETE 2017, 2019.
- [2018] Mrázek V., Sýs M., Vašíček Z., Švenda P., Sekanina L., Matyáš V.: Evolving Boolean Functions for Fast and Efficient Randomness Testing, In Proceedings of GECCO 2018, Genetic and Evolutionary Computation Conference, 2018.
- [2017] Sýs M., Klinec D., Švenda P.: The Efficient Randomness Testing using Boolean Functions, In Proceedings of SECRYPT 2017, 14th International Conference on Security and Cryptography, 2017.
- [2016] Sýs M., Říha Z., Matyáš V.: Algorithm 970: Optimizing the NIST Statistical Test Suite and the Berlekamp-Massey Algorithm, ACM TOMS Journal, 2016.
- [2015] Sýs M., Říha Z., Matyáš V., Márton K., Suciu A.: On the Interpretation of Results from the NIST Statistical Test Suite, ROMJIST Journal, 2015.
- [2014] Sýs M., Říha Z.: Faster randomness testing with NIST STS,SPACE 2014, Fourth International Conference on Security, Privacy, and Applied Cryptography Engineering, 2014.
Threshold Cryptography with Security-Certified Devices
Secure storage of secret key is paramount in cryptographic applications as the knowledge of the key directly corresponds to the ability of signing documents, decrypting messages, or confirming cryptocurrency transactions. To protect the secret keys, specialized cryptographic hardware like smartcards, HSM (hardware security module), or lately cryptocurrency wallets is used. However, due to implementation vulnerabilities, the private key may be still extracted even from the security-certified devices.
With the use of threshold cryptography, the risk of vulnerable implementations can be mitigated. Threshold cryptography allows for splitting of the secret key among multiple devices, which partake in an interactive protocol to perform cryptographic operations. The complete secret key is never reconstructed during this protocol, so if at least one of the devices remains uncorrupted, the secret key is not exposed. Our research focuses on threshold cryptography protocols executed on security-certified devices (smartcards, TPMs, cryptocurrency wallets).
Contact: Jan Kvapil kvapil@mail.muni.cz
More information, projects and resources:
- Threshold cryptography platform (MeeSign) Project website
- Bridge suite Project website
- Myst backdoor-resistant MPC platform web, Github repository
- Monero support on Trezor T, Github repository
Involved people:
- Jan Kvapil 2022-now (multi-party signing policies, verifiable computation)
- Jakub Janků 2019-now (threshold Schnorr for smartcards and TPMs, MeeSign client)
- Antonín Dufka 2019-now (threshold cryptography on smartcards, MeeSign platform)
- Petr Švenda 2018-now (project lead, some initial implementations)
Former members: Dušan Klinec 2018-2022 (Monero on Trezor T), Kristián Mika 2019-2024 (Bridge Suite, MPCOP for Raspberry Pi), Jiří Gavenda 2019-2022 (threshold ECDSA protocols)
Selected publications:
- [2025] Antonin Dufka, Peeter Laud and Petr Svenda: Two-party ECDSA with JavaCard-based smartcards, 23rd International Conference on Applied Cryptography and Network, Springer, 2025.
- [2024] Mariia Bakhtina, Jan Kvapil, Petr Svenda and Matulevicius Raimundas: The Power of Many: Securing Organisational Identity Through Distributed Key Management, In Advanced Information Systems Engineering (CAiSE), 2024.
- [2020] Dusan Klinec, Vashek Matyas: Privacy-Friendly Monero Transaction Signing on a Hardware Wallet, In IFIPSec 2020.
Bitcoin and related technologies
We analyze cryptographic aspects of implementations in Bitcoin and other cryptocurrencies with a focus on hardware wallets, privacy protocols, cryptographic implementations, and their failures. The goal is to make Bitcoin and selected cryptocurrency technologies better, more accessible, more private, and overall less vulnerable.
The work leverages our expertise in the side-channel analysis of cryptographic hardware (especially relevant for the hardware wallets), scrutiny of cryptographic implementations (both builder's and attacker's perspective), and randomness testing (crucial to have non-biased private keys and non-leaking signatures).
Contact: Petr Svenda svenda@fi.muni.cz
More information, projects and resources:
- Tools
- Daily-updated ecosystem insights
- CoinJoin analysis toolset, Github repository
- BlockSci (fork) adapted to CoinJoins, Github repository
- Weak keys detection and analysis
- Extraction of public keys from Bitcoin blockchain, Github repository
- Analysis of weak private keys and related transactions, J. Kubesa thesis
- Analysis of weak BIP32 seeds, D. Rajnoha thesis
- Software and hardware wallets
- Monero support on Trezor T, Github repository
- Building blocks of hardware wallets, A. Parak thesis
- Usability aspects of Bitcoin wallets, K. Raczova thesis
- Self-sovereign Identity Framework, F. Vass thesis
- CoinJoin privacy mixing protocols analysis
- Analysis of CoinJoin protocols (Wasabi 1.0, Whirlpoool), D. Varga thesis
- Analysis of CoinJoin protocols (Wasabi 2.0) D. Rypar thesis
- Simulation-based analysis of Whirlpool CoinJoin protocol D. Hlustik thesis
Involved people:
- Stanislav Bobon 2024-now (BlockSci extensions to CoinJoins)
- Antonín Dufka 2019-now (threshold cryptography)
- Jiri Gavenda 2024-now (Wasabi 2.x coinjoin analysis)
- Jan Kvapil 2022-now (key usage policies)
- David Rajnoha 2022-now (weak BIP32 seeds, JoinMarket analysis)
- Martin Seckar 2024-now (key usage policies)
- Milan Sorf 2022-now (analysis of hardware wallets)
- Petr Švenda 2019-now (project lead, some initial implementations, coinjoin-analysis toolchain)
Former participants: Stepan Yakimovich 2022-2023 (Bitcoin pub keys extraction), Dušan Klinec 2017-2022 (Monero on Trezor T, attack on Ledger's Monero); Filip Vass 2021-2022 (EU SSI framework); Denis Varga 2021-2022 (CoinJoin protocols analysis); K. Raczova 2020-2021 (usability of Bitcoin wallets); Adam Parak 2021-2022 (building blocks of hardware wallets); Jan Kubeša 2019-2022 (weak Bitcoin EC keys);
Selected publications:
- [2026] Petr Svenda, Jiri Gavenda, Vasilios Mavroudis, Chris Hicks: CoinJoin ecosystem insights for Wasabi 1.x, Wasabi 2.x and Whirlpool coordinator-based privacy mixers, In Proceedings of the Privacy Enhancing Technologies Symposium (PETS'26), 2026.
- [2025] Jiri Gavenda, Petr Svenda, Stanislav Bobon, Vladimir Sedlacek: Analysis of input-output mappings in coinjoin transactions with arbitrary values, In Proceedings of the 30th European Symposium on Research in Computer Security (ESORICS), 2025.
- [2025] Milan Šorf, Petr Švenda, Lukasz Chmielewski: Large-scale security analysis of hardware wallets, In Availability, Reliability and Security (ARES/TRUSTBUS), 2025.
- [2022] Antonin Dufka, Vladimir Sedlacek, Petr Svenda: SHINE: Resilience via Practical Interoperability of Multi-party Schnorr Signatures, In Proceedings of the 19th International Conference on Security and Cryptography (SECRYPT), 2022.
- [2020] Dusan Klinec, Vashek Matyas: Privacy-Friendly Monero Transaction Signing on a Hardware Wallet, In Proceedings of IFIPSec'20, 2020.
Open-source security tools
We believe that the open-source security tools are crucial not only for the general accessibility, but also to produce more robust secure software and hardware products and their more transparent security certifications. Not only the dedicated testing laboratories, but also end-users shall be able to replicate majority of the steps carried during the certification like Common Criteria or FIPS140-2.
Existing certification process produces trove of interesting, but hard to automatically process data. We extract, process and analyze these datasets to aid quick identification of potentially vulnerable products, provide ecosystem insight, and reason about the overall state of security. Majority of our other research results are accompanied with open-source tooling. We now focus on putting pieces together, connecting certified devices with its metadata obtained by open-source tools and shared via open, transparent network.
Contact: Petr Švenda svenda@fi.muni.cz
More information, projects and resources:
- sec-certs sec-certs - analysis of Common Criteria and FIPS140 security certificates
- JCAlgTest GitHub repository - tools for thorough testing of smart card capabilities
- TPMAlgtest GitHub repository - tools for thorough testing of TPM capabilities
- SCRUTINY GitHub repository - hardware and software security testing and reference profile comparison tools.
Involved people:
- Ján Jančár 2018-now (security certificates analysis)
- Martin Ukrop 2022-now (sec-certs projects lead)
- Adam Janovský 2020-now (security certificates analysis)
- Petr Švenda 2019-now (security certificates analysis, continuous certification tools)
- Łukasz Chmielewski 2023-now (Common Criteria insights)
Past members: Lukáš Němec 2019-2022 (existing open-source tools), Milan Brož 2019-2025 (disk encryption, TPM analysis)
Selected publications:
- [2025] Revisiting the analysis of references among Common Criteria certified products, Adam Janovsky, Lukasz Chmielewski, Petr Svenda, Jan Jancar and Vashek Matyas, Computers and Security journal vol.152, 2025.
- [2024] Janovsky, A., Jancar, J.; Svenda, P.; Chmielewski, L.; Michalik, J.; Matyas, V.: sec-certs: Examining the security certification practice for better vulnerability mitigation, In Computers and Security journal vol.143, 2024.
- [2024] Jancar, J.; Suchanek, V.; Svenda, P.; Sedlacek, V.; Chmielewski, L.: pyecsca: Reverse engineering black-box elliptic curve cryptography via side-channel analysis, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2024. Received Honorable mention and Best artifact awards.
- [2024] Svenda, P.; Dufka, A.; Broz, M.; Lacko, R.; Jaros, T.; Zatovic, D.; Pospisil, J.: TPMScan: A wide-scale study of security-relevant properties of TPM 2.0 chips, In IACR Transactions on Cryptographic Hardware and Embedded Systems (CHES) 2024.
- [2022] Petr Svenda, Rudolf Kvasnovsky, Imrich Nagy and Antonin Dufka: JCAlgTest: Robust identification metadata for certified smartcards, In SECRYPT'22
- [2020] Vasilios Mavroudis, Petr Svenda: JCMathLib: Wrapper Cryptographic Library for Transparent and Certifiable JavaCard Applets, In Proceedings of CyberCert'20, IEEE Security&Privacy Workshops, IEEE, 2020.
Side-channel analysis
We are focused on side-channel analysis (SCA) of public-key cryptosystems, including post-quantum (PQ) schemes, and on hardware attacks against real-world devices. A core theme is leveraging state-of-the-art techniques, like deep learning, to push the limits of SCA against both symmetric and asymmetric algorithms, and to rigorously evaluate and harden implementations deployed in practice.
Contact: Lukasz Chmielewski chmiel@fi.muni.cz
More information, projects, and resources:
- Attack_Kyber_ACNS2024 GitHub repository - an online template attack against Kyber (ML-DSA).
- GitHub repository - three implementations of X25519 in C and assembly for the Cortex-M4 with countermeasures against side-channel and fault injection attacks.
Involved people:
- Łukasz Chmielewski 2022-now (side-channel and fault injection security)
- Milan Šorf 2023-now (side-channel analysis and crypto-wallets security)
- Veronika Hanulíková 2025-now (side-channel security of JavaCard and blockchain security)
- Master students: Tomáš Jaroš, Michal Masrna, and Oliver Bajus
- Jan Janásek
- Oliver Šimoník
Past members: master students: Daud Naveed, Lubomír Hrbáček, and Radomír Mann.
Selected publications:
- Péter Horváth, Łukasz Chmielewski, Lejla Batina, Léo Weissbart, and Yuval Yarom: BarraCUDA: Edge GPUs do Leak DNN Weights, in Proceedings of the 34th USENIX Security Conference 2025.
- Estuardo Alpirez Bock, Gustavo Banegas, Chris Brzuska, Łukasz Chmielewski, Kirthivaasan Puniamurthy, Milan Šorf: Breaking DPA-protected Kyber via the pair-pointwise multiplication, in Proceedings of the Applied Cryptography and Network Security (ACNS) conference, Springer Nature, 2024.
- Péter Horváth, Łukasz Chmielewski, Lejla Batina, Léo Weissbart, and Yuval Yarom: CNN architecture extraction on edge GPU, in Proceedings of Artificial Intelligence in Hardware Security (AIHWS) Workshop affiliated with ACNS, Springer Nature, 2024.
Usable security
Our usable security projects focus on computer security and interactions of systems with end-users (true end-users as well as IT professionals using a particular system for their job). We are currently investigating factors influencing usability of reports from penetration testing, figuring out what those that use these reports can and cannot really find out from pentesting reports - and how to improve that. We also examine usability of AI-assisted pentesting report writing.
We started our first significant project in the area of usable security in 2014, in cooperation with three industrial partners, Faculty of social studies, and Faculty of law. The project aimed to identify influences that make users change their risky behavior to more secure one. Four sets of experiments ran in cooperation with commercial companies (ESET, Netsuite and SodatSW). Every experiment targeted a different target group and used a different technique (warning, security dialogue, e-learning, user-friendly password recovery, etc.). This project was unique for the cooperation of three different faculties of MU and three commercial companies, who wanted to understand their users better and increase their products' overall security by improving interfaces and processes used by their end-users. We also finished a project in cooperation with the Faculty of social studies and AHEAD Itec/Monet+ company. It aimed at user testing of selected authentication methods (NFC token, smart card with card reader, fingerprint and PIN code) with results available here
Archived research projects in CRoCS laboratory
Disk encryption
 The first goal is research, and implementation of new algorithms (key derivation, authenticated encryption or integrity protection mechanism) into existing open-source LUKS/cryptsetup disk encryption project.
The first goal is research, and implementation of new algorithms (key derivation, authenticated encryption or integrity protection mechanism) into existing open-source LUKS/cryptsetup disk encryption project.
The second goal is to make LUKS/libcryptsetup (and supported FDE formats) truly multiplatform tool (Windows/Linux) with focus to independent and extensible open-source software based FDE (Full Disk Encryption) solution.
Last update: 22.01.2021
Contact: Milan Brož xbroz@fi.muni.cz
- Research project internal wiki pages
- Upstream (Linux) project homepage, GitHub mirror
Join us! The possible areas for cooperation:
- Developing HMI (Human-machine interface) for storage encryption - ease of use, test cases, simple GUI, HMI usability experiments.
- Disk (sector-level) storage encryption in Windows study, existing approaches and implementations (TrueCrypt, DiskCryptor, Bitlocker, FreeOTFE, …) with focus on free and open-source solutions. Windows driver architecture for implementing similar encryption capabilities as provided in Linux dm-crypt module.
- Windows boot process analysis and possibilities to use open-source boot loaders like GRUB2 to inject boot of core Windows system from (LUKS) encrypted device.
- Using open-source multiplatform encryption libraries (gcrypt, openssl, etc) for implementation of symmetric block cipher encryption wrappe in windows environment, both in userspace and driver.
- Current status quo in RNG available in Windows7 and later systems, implementation of wrapper (or usable alternative) to Linux /dev/[u]random device.
- Milan Brož 2014-now (Project lead and coordinator, Red Hat cooperation, grumbling)
- Ondrej Mosnáček 2015-now
- Agáta Dařbujanová 2014-2016 (Student, User interface for storage encryption application)
Selected publications:
- [2016] Harčár, M.: Generátory náhodných čísel v multiplatformním prostředí, FI bachelor thesis
- [2016] Dařbujanová, A.: Uživatelské rozhraní aplikace pro šifrování disku, FI bachelor thesis
- [2016] Brož M.,Kozina,O.: The Future of Disk Encryption with LUKS2, DevConf 2016
- [2015] Brož M.,Matyáš V.: Selecting a New Key Derivation Function for Disk Encryption, STM 2015
- [2015] Mosnáček, O.: Key derivation functions and their GPU implementations, FI bachelor thesis
- [2014] Brož M.,Matyáš V.: The TrueCrypt On-Disk Format—An Independent View, IEEE Security & Privacy, 2014, vol. 12, No 3, p. 74-77. ISSN 1540-7993
- [2011] Brož M.:Disk encryption (not only) in Linux, Europen.cz 2011, Red Hat DevConf 2012
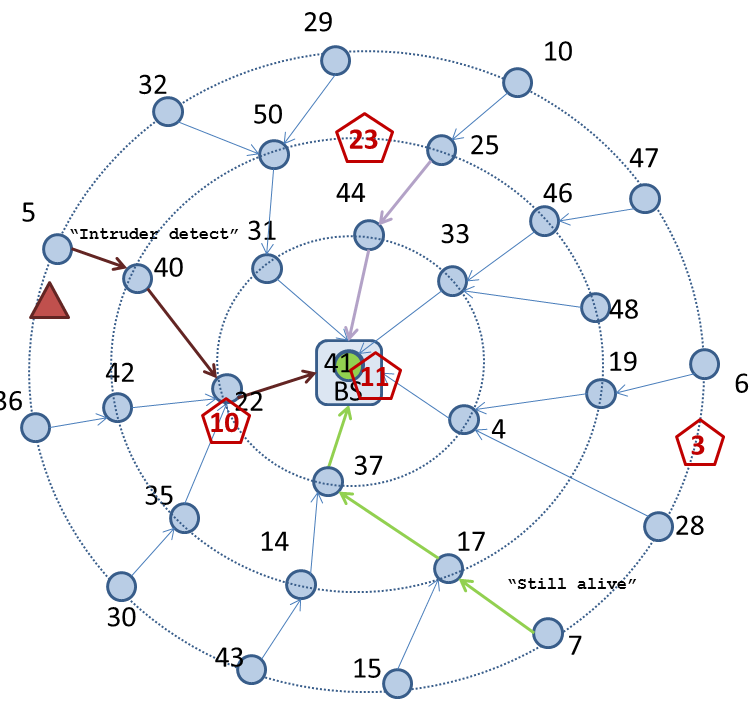
Wireless Sensor Networks
This project includes providing a secure platform that is transparent for applications in wireless sensor networks (WSN) - WSNProtectLayer. Our platform includes intrusion detection system (IDS) detecting active attacks. We consider privacy issues to prevent passive attacks on the WSN. We also propose secrecy amplification protocols and evaluate key management schemes. Current work includes parametrised attacker simulated on KMSforWSN framework.
Last update: 17.5.2018
Contact: Lukáš Němec lukas.nemec@mail.muni.cz
Additionally, we are developing an optimization framework for the IDS incorporating MiXiM simulator. Evolutionary algorithms are used to optimize the IDS's performance.
- Research project internal wiki pages
- WSNProtectLayer - security middleware for TinyOS
- virtual radio is simulated and automatic packet protection, IDS and key management is provided.
- WSNProtectLayer Github repository
- Take a look at video showing WSNProtectLayer middleware in action.
- Secrecy amplification protocols
- establishing secure links in partially compromised network
- SensorSim simulator download page - fast simulator optimized for simulation of secrecy amplification protocols and probabilistic key predistribution
- KMSforWSN framework based on OMNet++ simulator together with parametrised attacker specification
- Laboratory testbed
- Laboratory tesbed with 28 TelosB and 20 JeeNode nodes
- Lukáš Němec 2013-now (Crypto and Key management in TinyOS, Arduino testbed network, Edu-hoc)
- Radim Ošťádal 2013-now (Secrecy amplification protocols, parametrised attacker in)
- Petr Švenda 2004-now (Key management schemes, secrecy amplification protocols)
Former participants: Martin Stehlík 2010-2017 (IDS, simulators, optimization); Marek Sýs 2015 (secrecy amplification protocols); Filip Jurnečka 2010-2014 (Key management schemes), Marcel Gazdík 2012-2013 (ePIR&RFID hw readers), Dušan Klinec 2008-2014 (WSNProtectLayer core developer, a lot of network experiments), Jiří Kůr 2009-2014 (Privacy protection, key establishment), Tobiáš Smolka (testbed, omnetpp experiments, secrecy amplification), Andriy Stetsko (IDS in WSN)
Selected publications:
- [2019] Němec, L.; Matyáš, V;Ošťádal, R.; Švenda, P.; Palant P.-L.: Evaluating Dynamic Approaches to Key (Re-)Establishment in Wireless Sensor Networks, Sensors, 19-4, 2019
- [2018] Němec, L.; Ošťádal, R.; Švenda, P.; Matyáš, V.: Adaptive Secrecy Amplification with Radio Channel Key Extraction, 2018 14th International Conference on Distributed Computing in Sensor Systems (DCOSS), 2018.
- [2018] Němec, L.; Ošťádal, R.; Švenda, P.; Matyáš, V.: Entropy Crowdsourcing – Protocols for Link Key Updates in Wireless Sensor Networks, In 26th International Workshop on Security Protocols (SPW 2018). Lecture Notes of Computer Science. Springer.
- [2016] Ošťádal, R.; Švenda, P.; Matyáš, V.: Reconsidering Attacker Models in Ad-hoc Networks, In 24th International Workshop on Security Protocols (SPW 2016). Lecture Notes of Computer Science. Springer.
- [2015] Ošťádal, R.; Švenda, P.; Matyáš, V.: On Secrecy Amplification Protocols, In 9th WISTP International Conference on Information Security Theory and Practice, LNCS 9311, Springer, pp. 3-19, 2015.
- [2014] Ošťádal, R.; Švenda, P.; Matyáš, V.: A new approach to secrecy amplification in partially compromised networks, In 4th International Conference on Security, Privacy and Applied Cryptography Engineering, LNCS 8804, Springer, pp. 92–109, 2014.
Software Security and Secure Programming
This project focuses on usage, evaluation and extension of various tools related to secure programming, application vulnerabilities, security testing and code review. We are interested in static and dynamic analysis of applications with a special focus on security bugs, fuzzy testing, taint analysis and semi-automated review procedures and its incorporation into application development lifecycle. This project is coordinated with Y Soft Corporation, a.s., and for students participating in this project, there is a possibility to get a financial support from this company. More general information about Y Soft cooperation with students can be found here.
Last update: 19.09.2018
Contact: Andriy Stetsko xstetsko@fi.muni.cz or andriy.stetsko@ysoft.com
Financial support: Y Soft Corporation, a.s. will provide financial support (in a form of stipend at the faculty or a part-time job in the company) to students with promising results.
Possible topics for cooperation with bachelor students:
Possible topics for cooperation with master students:
- Andriy Stetsko 2012-now (Project coordinator, thesis supervisor, Y Soft Corporation, a.s.)
Previous research topics:
- 2013-2017: Tools for dynamic security analysis of web applications, financial support from Y Soft Corporation
- 2015-2016: Analysis and application of OWASP testing guide, financial support from Y Soft Corporation
- 2015-2016: Metasploit, financial support from Y Soft Corporation
- 2014-2016: Secure software development processes, financial support from Y Soft Corporation
- 2012-2016: Tools for static and dynamic code analysis, financial support from Y Soft Corporation
- 2014-2015: Security mechanisms of PDF files
- 2014-2015: Security aspects of Xamarin/Android Platform
- Cesta project - security-related transformations of JavaCard source code, financial support from Y Soft Corporation
Faster randomness testing
This project is focused on improving the implementation of standard empirical test of randomness since some complete tests (Linear Complexity, Spectral, Overlapping template matching) can take hours on standard computer for usual amount of data. Tests are usually grouped into test batteries (NIST STS, Diehard,TestU01) to provide more complex randomness analysis. Currently we are focusing on optimization of NIST STS battery. Visit our online testing service.
Last update: 27.09.2016
Application Project Github repository
- Zdenek Říha 2013-now (Performance testing) zriha@fi.muni.cz;
- Marek Sýs 2013-now (Algorithm analysis) syso@mail.muni.cz
Publications
- [2015] Sýs, M.; Z. Říha, V. Matyáš, K.Márton, A. Suciu: On the Interpretation of Results from the NIST Statistical Test Suite, ROMJIST Journal, 2015.
- [2014] Sýs, M.; Z. Říha: Faster randomness testing with NIST STS,SPACE 2014, Fourth International Conference on Security, Privacy, and Applied Cryptography Engineering, 2014.
Attacker strategy evolution (GANet)
Last update: 08.01.2016
Contact: Zdenek Říha zriha@fi.muni.cz
Project description: This project focuses on automated generation of attacker's strategies against real implementation of various network applications. Currently, we aim to optimize existing Denial of Service attacks (DoS attacks, Link) in order to achieve maximum impact on the victim webserver. GANet contains source codes we are using - for now, combination of OS apps (Perfmon,…) and Python scripts.
- Research project internal wiki pages
- Project Github repository, wiki pages
- Zdenek Říha 2016-now (?) zriha@fi.muni.cz;
- Víťa Bukač 2014-now (preparation of HTTP DOS experiments, VM preparation, initial Python implementation)
- Radim Ošťádal 2014-now (preparation of HTTP DOS experiments)
- Petr Švenda 2014-now (gibbering)
Former participants: Tatevik Baghdasaryan 2014-2015 (testing simple web server);
Selected publications
- [2015] Bukač, V.; Ošťádal, R.; Švenda, P.; Baghdasaryan, T. and Matyáš, V.: Challenges of fiction in network security - perspective of virtualized environments, LNCS 9379, pp. 145-151, Springer, 2015.
- [2014] Bukač, V.; Lorenc, V. and Matyáš, V.: Red Queen's Race: APT win-win game. In Security Protocols XXII - 22nd International Workshop, Revised Selected Papers, LNCS 8809, pp. 55-61, Springer, 2014.
Whitebox cryptography
Last update: 14.9.2015
Status: Completed/On hold
Contact: Petr Švenda svenda@fi.muni.cz
Project description: This project is focused on design and development of the special implementations of cryptographic functions able to operate in an environment under full control of an attacker and still able to protect used secrets (e.g., encryption keys).
- Research project internal wiki pages
- SecureFW framework for source codes and binaries - earlier version of whitebox AES implementation in Cpp, secure channel with JavaCard smart card
- Explanation of whitebox cryptography, homomorphic encryption and computation with encrypted function/data: slides
- List of resources related to whitebox cryptography
- Lenka Bačinská 2012-now (Whitebox AES)
- Petr Švenda 2008-now (project lead, whitebox AES with smartcards)
Former participants: Marián Čečunda 2013-2015 (Whitebox RSA, HMAC, Keccak); Dušan Klinec 2012-2014 (whitebox AES implementation, attacks);
Selected publications
- [2015] Bačinská, L.: White-box attack resistant cipher based on WBAES, Master thesis, Masaryk university, 2015.
- [2015] Čečunda, M.: Návrh implementace algoritmů RSA a HMAC pomocí whitebox kryptografie, Master thesis, Masaryk university, 2015.
- [2013] Klinec, D.: White-box attack resistant cryptography, Master thesis, Masaryk university, 2013.
DDoS-as-a-Service landscape
Last update: 14.1.2016
Status: Completed/On hold
Contact: Vít Bukač xbukac@fi.muni.cz
Project description: We want to map the dark economy behind Denial-Of-Service attack services (DDoSaaS) for hire, the communication between DDoSaaS providers and customers and collect samples of attack traffic from real existing DDoS services. This project is about getting hands-on experience with network attacks in real environment instead of in closed labs, analyzing often neglected economy aspect of network attacks and dipping into the mindset of a cyber-criminal.
- Research project internal wiki pages
- Vít Bukač 2014-2015 (Coordinator)
- Vlasta Šťavová 2014-2015 (Social aspects)
- Lukáš Němec 2014-2015 (Technical aspects)
- Zdeněk Říha 2015 (Technical aspects)
- Lukáš Šrom 2014 (Technical aspects)
Publications
- [2015] Bukač, V.; Šťavová, V.; Němec, L.; Říha, Z. and Matyáš, V.: Service in denial – clouds going with the winds, In Proceedings of NSS 2015, 9th International Conference on Network and System Security, LNCS 9408, pp. 130-147, Springer, 2015.
- [2015] Bukač, V. and Matyáš, V.: Analyzing traffic features of common standalone DoS attack tools, In Proceedings of SPACE 2015, 5th International Conference on Security, Privacy, and Applied Cryptography Engineering, LNCS 9354, pp. 21-40, Springer, 2015.
- [2015] Bukač, V.; Říha, Z.; Šťavová, V. and Matyáš, V.: DDoSaaS: DDoS jako služba, In IS2: From trends to solutions, pp. 35-39, Tate International, 2015.
Android Security
Last update: 14.10.2014
Status: Completed/On hold
Contact: Zdeněk Říha zriha@fi.muni.cz ; Dušan Klinec ph4r05@mail.muni.cz
Project description: These activities look at the security issues of the Android installation files (APK). The Android APK files are digitally signed, but the signer can be anybody. Therefore it is possible to to modify the APK files (to include malware, for example) and resign it. This can be done in an automated way. Such a modification/infection can also be done online in the form of the man-in-the-middle attack where the APK package is transparently modified on its way from the server towards the mobile device if no encryption of the communication is done.
- Zdenek Říha 2012-now
- Dušan Klinec 2014-now
Former participants: Jan Svoboda (2013-2014), Eduard Cihuňka (2013-2014)
Selected publications






















Contact: Vashek Matyáš matyas@fi.muni.cz
Involved people:
Former participants: Radim Janča (2014-2016); Lydia Kraus (2018-2020); Kamil Malinka (2013-2016); Vlasta Bukačová (Šťavová) (2014-2019); Martin Ukrop (2016-2024); Lenka Knapová (2018-2020)
Selected publications: