Reconsidering Attacker Models in Ad-hoc Networks - SPW 2016
Authors: Radim Ostadal, Petr Svenda, Vaclav Matyas
Abstract: Our paper aims to move the research of secrecy amplification protocols for general ad-hoc networks to more realistic scenarios, conditions and attacker capabilities. The extension of the current attacker models is necessary, including the differentiation based on types of attacker's manipulation with a node, monitoring capabilities and movement strategies. We also aim to propose suitable secrecy amplification protocols that can reflect the new attacker models in different examined scenarios, utilising genetic programming and manual post-processing.
- Conference page: SPW 2016
- Download author pre-print of the paper: pdf
- Download presentation: pdf
- Download used simulator: zip source code
- Download simulator documentation: zip html documentation
Bibtex:
@inproceedings{attackermodels_spw2016,
author = {Radim O\v{s}\v{t}\'{a}dal \Petr \v{S}venda \and V{\'a}clav Maty{\'a}\v{s}},
title = {Reconsidering Attacker Models in Ad-hoc Networks},
booktitle = {24th International Workshop on Security Protocols (SPW 2016)},
year = {2016},
publisher = {{\em To appear in Lecture Notes of Computer Science.} Springer}
}
What is this paper about?
Ad-hoc networks often handle highly sensitive information and security of such networks is a typical baseline requirement. Secure link communication is the building block for many security services maintained by a network. Ad-hoc networks also present several challenges like limited computational and storage resources or an energy source, usually in the form of a battery.
The attacker in that environment is usually able to capture a node itself and read out all keying material as there typically is no tamper resistance. After the initial compromise, the global attacker is expected.
The secrecy amplification (SA) protocols were proposed to re-secure some previously compromised communication links using non-compromised paths to deliver new secure keys. The comprehensive overview of SA protocols could be found here.
In this paper, we:
- Provided three additional attacker models compared to the one used (Random Key compromise): key exfiltration model, passive node control model, and active node control model. Based on attacker capabilities, we also distinguish the global and local attacker.
- Proposed different ways of evaluation of SA protocols: a ratio of compromised and non-compromised link keys, a percentage of secure communication among neighbours, or the percentage of secure communication from nodes to the base station.
- Extended the KMSforWSN framework. The whole framework including the documentation could be download here.
- Discussed different attacker capabilities and behaviour to parametrise the attacker.
- Performed an initial comparison of a local and global attacker on Random key compromise and Random node compromise pattern.
- Performed an experiment for Passive node control model.
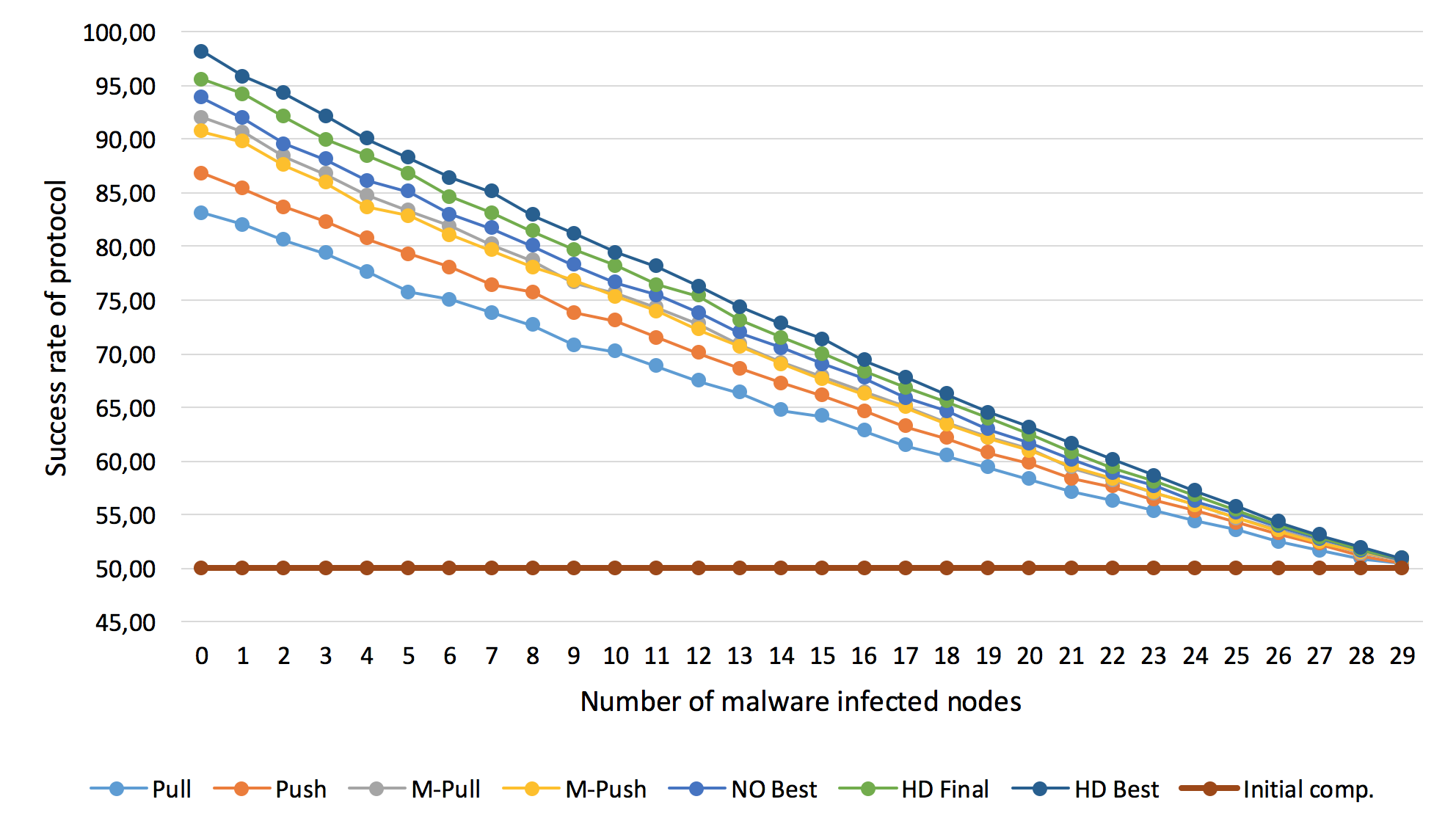
A success rate of SA protocols for a different number of malware infected nodes. A decrease in the percentage of secured links is linear that is good considering the attacker's control over the node. One can obtain reasonably secure network (more than 85% of secure links) even in case of 7 malware infected nodes considering the hybrid designed protocols are used.